Your product is pitched as a cure for the perennial IT headache of Shadow IT. But just bear in mind that when it comes to ordinary business users, some types of medicine are more palatable than others. Being hit with a stark “computer says NO” when you’re trying to fix an everyday business problem can leave a particularly bitter taste.
For shadow IT solutions, there’s a sweet spot – and a potentially very useful differentiator – that’s easy to overlook.
Of course your licensing management tool should give tech teams the visibility and control they expect. But if it also speaks to the sensibilities and practical needs of endpoint users, you can better pitch it as a way for IT to build stronger relationships across the enterprise. And at a time when many CTOs are working hard to establish their credentials as true partners to the wider business, this is all to the good.
To help you consider this, here’s a fresh look at shadow IT from technical governance and business user perspectives – and at how a more sensitive approach to product development could result in a more effective and compelling product offering.
Shadow IT Definition:
“Shadow IT is any software, hardware or IT resource used on an enterprise network without the IT department’s approval, and often without IT’s knowledge or oversight.” (IBM)
Shadow IT as a business issue: the technical leader’s perspective
Not so long ago, the IT department was an employee’s first port of call whenever they needed a technical fix for a business-related problem. The technical team would source a solution, check that it’s safe, distribute, install and configure it – and the user would then be good to go.
But thanks in no small part to the proliferation of cloud-based offerings, IT has been effectively consumerised and democratised.
An employee might need a quick-and-easy project-management aid, a cool way to visualise a stack of financial data, or even a generative AI tool to write this month’s report to the board. They know “there’s an app for that”, find it in the store, ping in the company credit card number, and hey presto: problem solved – without any involvement from IT whatsoever, and without the technical jobsworths even needing to know.
From an IT perspective however, risks and complications abound…
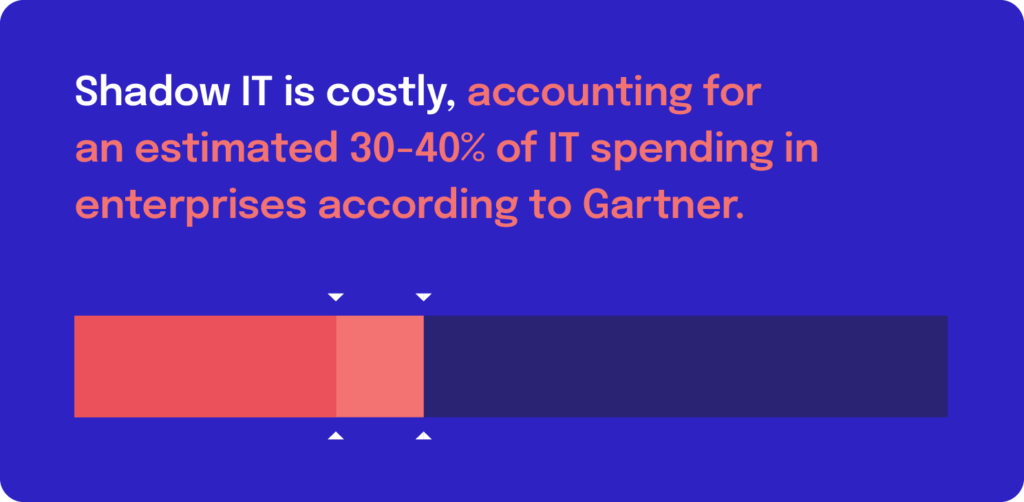
Shadow IT is costly, accounting for an estimated 30-40% of IT spending in enterprises according to Gartner.
The real problem here is the potential waste involved. Let’s face it; when an employee is looking for a quick fix from an app, value-for-money isn’t always front of mind. And if multiple employees are purchasing the same software (and in some cases, hardware and peripherals) independently, there’s the issue of duplication, along with potential failure to get the best licensing deals. In fact, one estimate suggests that the average company wastes $135,000 a year on unnecessary license spending.
Then there are the multitude of governance and security issues that shadow IT can give rise to. What personal information is being exposed through that unauthorised HR tool? Where will data reside – and is it GDPR-compliant? What’s the source for this video editing app – and is it legitimate?
An absence of oversight and control linked to shadow IT can have severe business implications. According to IBM, the global average cost of a data breach in 2023 was $4.45 million – 15% more than in 2020. Further down the food chain, an estimated 60% of small businesses close within six months of a significant security breach.
Shadow IT: the employee perspective
No doubt, your customer’s IT team has a policy in place stipulating that unauthorised installs are forbidden. But 83% of IT teams say that trying to enforce these types of security policies is an impossible job. Around half of departments say they don’t want IT telling them what to use. So why might that be?
Gartner has recently started referring to a desire for what it calls radical flexibility among employees. The Covid imperative granted a lot more freedom in when and where work was done. And incidentally, 80% of IT professionals get pushback from employees who don’t like controls when they’re working from home. But a couple of years on from the pandemic, employees also crave much greater agency in how the work gets done.
Resourceful employees have a tendency to conveniently forget or seek to circumvent shadow IT rules and control measures if it stops them getting the job done. If your licensing management tool is to really prove its worth, it’s definitely worth finding ways to address the typical employee mindset, and embedding features that reduce user frustration.
More of the carrot, less of the stick? Nudging users towards shadow IT compliance
Robust, enterprise-grade, licensing management versus a frictionless experience for consumers of business technology. These two concepts are not mutually exclusive. You can and should aim to deliver both.
So how might this be achieved?
One approach to ensure that any technical restrictions are accompanied by functionality designed to meet end-user needs (and mitigate frustration!). In other words, for every hard-and-fast restriction, make sure there’s a ‘carrot’ (or a nudge) to maximise compliance.
Here are a few examples:
Access to tech
The restriction: Only IT-approved assets are permitted within the customer’s network
The nudge to compliance:
👉 An easy-to-search catalogue of existing tools available already across the network. (Chances are, if the user needs a fix for a business problem, something suitable is in the tech stack already).
👉 A bank of resources providing guidance on how to identify appropriate tools for different tasks.
Troubleshooting
The restriction: Prior permission must be sought from IT before any new asset is deployed. Issues with licensing must be addressed through IT.
The nudge to compliance:
👉 An easy-to-use platform for requests to be submitted to IT.
👉 IT to have the ability to check the status of subscriptions at-a-glance and respond to requests / queries as swiftly as possible.
Payments
The restriction: IT and/or Finance to have ultimate control over payments for IT purchasing/licensing.
The nudge to compliance:
👉 ‘Ultimate control’ does not have to mean micromanagement. By integrating embedded payment functionality into your product, it opens up the possibility of delegating payment permissions to business users, granting them greater autonomy, in for example, scaling capacity as and when needed, and acquiring add-ons to existing services.
What next?

One remaining question worth addressing is whether IT managers are actually bothered about a ‘carrot’ or a ‘nudge’ when it comes to addressing shadow IT. Are they not just solely interested in a big stick?
The answer to that is ‘Not really’. 63% of tech leaders struggle to communicate IT’s value to the wider business – and that’s becoming a real worry to a lot of them. CIO Magazine and other voices in this space speak frequently about the desire to improve business intimacy, show their relevance and deliver business value. If you’re seen primarily as a blocker rather than an enabler, it’s much harder to do this.
In short, if you can go beyond the big stick to offer a more nuanced approach with licensing management, you’re more likely to be on the same page as your target audience.




